Most email breaches in 2026 don’t involve brute force. They involve a convincing email that someone clicked, a shared inbox that nobody was watching, or an OAuth permission that was granted and forgotten.
This guide covers the email security best practices that matter most in 2026, updated for AI-generated phishing, MFA fatigue attacks, and the platform-specific controls available in Gmail, Outlook, and Microsoft 365. It also covers what most security checklists skip: the operational layer, meaning how teams actually monitor, audit, and respond to threats across shared inboxes at scale.
Table of Contents
- What’s new in 2026
- Core email security best practices that remain non-negotiable
- The security risk most teams overlook
- Best practices for auditing your email security setup
- Email security best practices for employees: what training should actually cover
- Building a security-first email culture
- References
What’s new in 2026
The basics of email security haven’t changed. Phishing, weak passwords, unencrypted data in transit: these remain the leading causes of email-related breaches. What has changed is the sophistication of the attacks, the platforms they target, and the habits people have developed around data sharing.
the generation that refused to accept cookies.
— Wise (@trikcode) March 25, 2026
is now giving AI access to their desktops, files, and bank accounts.
There’s a certain irony in the fact that a generation of users trained to decline cookies is now uploading contracts, customer records, and internal communications to AI tools without a second thought.The threat surface didn’t just grow , it moved. And email sits right at the center of it
- AI-generated spear phishing. Attackers can now use publicly available information, LinkedIn profiles, company blogs, press releases, to generate highly personalized phishing emails at scale. These aren’t generic “Dear User” messages. They reference real colleagues, recent projects, and legitimate-sounding requests. Standard email filters trained on historical attack patterns aren’t designed to catch them.
- OAuth and app permission abuse. In Gmail and Microsoft 365 environments, attackers are increasingly targeting third-party app integrations rather than account passwords. A malicious app granted OAuth access to a calendar or email account can exfiltrate data without triggering a password-based login alert. This is now a documented attack vector in both platforms.
- QR code phishing (quishing). Images embedded in emails containing QR codes bypass most text-based email security filters. The QR code redirects the user to a credential-harvesting page. Because the threat is image-based, many enterprise email security tools miss it entirely.
- MFA fatigue attacks. Attackers who have obtained valid credentials now flood targets with MFA push notifications until the user approves one out of frustration or confusion. This has compromised organizations even where 2FA was properly enabled.
Recommended reading
Core email security best practices that remain non-negotiable
The following controls form the baseline of corporate email security best practices. If any of these aren’t in place, newer threats aren’t the priority. Fix the foundation first.
1. Strong, unique passwords and a password manager
Weak or reused passwords remain among the most common entry points in corporate email compromises. Email password security best practices in 2026 mean using a password manager to generate and store unique credentials for every account.
Bitwarden, 1Password, and Dashlane are all reliable options.
The goal is straightforward: no two accounts should share a password, and no password should be something a person can memorize or predict.
2. Multi-factor authentication, done dight
MFA is essential. But SMS-based MFA is no longer sufficient for corporate accounts. SIM-swapping attacks can intercept one-time codes. The stronger options are authenticator apps such as Google Authenticator, Authy, or Microsoft Authenticator, or hardware keys like YubiKey.
To counter MFA fatigue attacks specifically: configure number matching in Microsoft Authenticator, where the user must enter a number shown on screen rather than just tapping “Approve.” In Google Workspace, phishing-resistant FIDO2 keys are available and recommended for privileged accounts.
3. Attachment security: scan, restrict, and train
Email attachment security best practices in 2026 go beyond virus scanning. Most enterprise-grade environments, including Gmail with Google Workspace and Outlook with Microsoft 365 Defender, now offer sandbox analysis that executes attachments in a safe environment before they reach the inbox. This should be enabled by default, not left as an optional configuration.
! Password-protected ZIP files are increasingly used to bypass attachment scanners. Any unexpected compressed file should trigger the same level of suspicion as an unknown executable.
4. Verify the sender address, not just the display name
Display name spoofing is trivial to execute. An email appearing to come from “Your CFO – Michelle” can originate from an address with no relationship to your organization whatsoever. In Outlook and Gmail, hovering over the sender name reveals the actual address. For high-stakes requests such as wire transfers, vendor payment changes, or access grants, always verify over the phone using a known number before acting. No legitimate financial instruction should be processed solely on the basis of an email.
5. Keep software and email clients updated
ttackers actively scan for organizations running outdated software. A known vulnerability in an older version of Outlook or a legacy email gateway is a documented attack vector, not a theoretical one.
This is why effective patch management is critical for maintaining email security and reducing exposure to cyber threats. For teams on Microsoft 365 or Google Workspace, platform-level updates are managed centrally, but local clients, plugins, and browser extensions that connect to email accounts also need continuous monitoring and timely patching. Deferred updates create exploitable windows that attackers
Recommended reading
6. Encrypt Sensitive Emails in Transit and at Rest
Most major email providers, including Gmail, Outlook, and Yahoo Mail, enforce TLS encryption for emails in transit. For emails containing sensitive business information such as contracts, financial data, or personally identifiable information, end-to-end encryption adds a necessary layer.
In a Microsoft 365 environment, Microsoft Purview Message Encryption allows organizations to send encrypted messages to anyone, including external recipients using non-Microsoft clients. In Google Workspace, S/MIME is available for enterprise plans and encrypts content so that only the intended recipient can read it. For teams with compliance requirements, these controls are table stakes, not optional extras.
The security risk most teams overlook
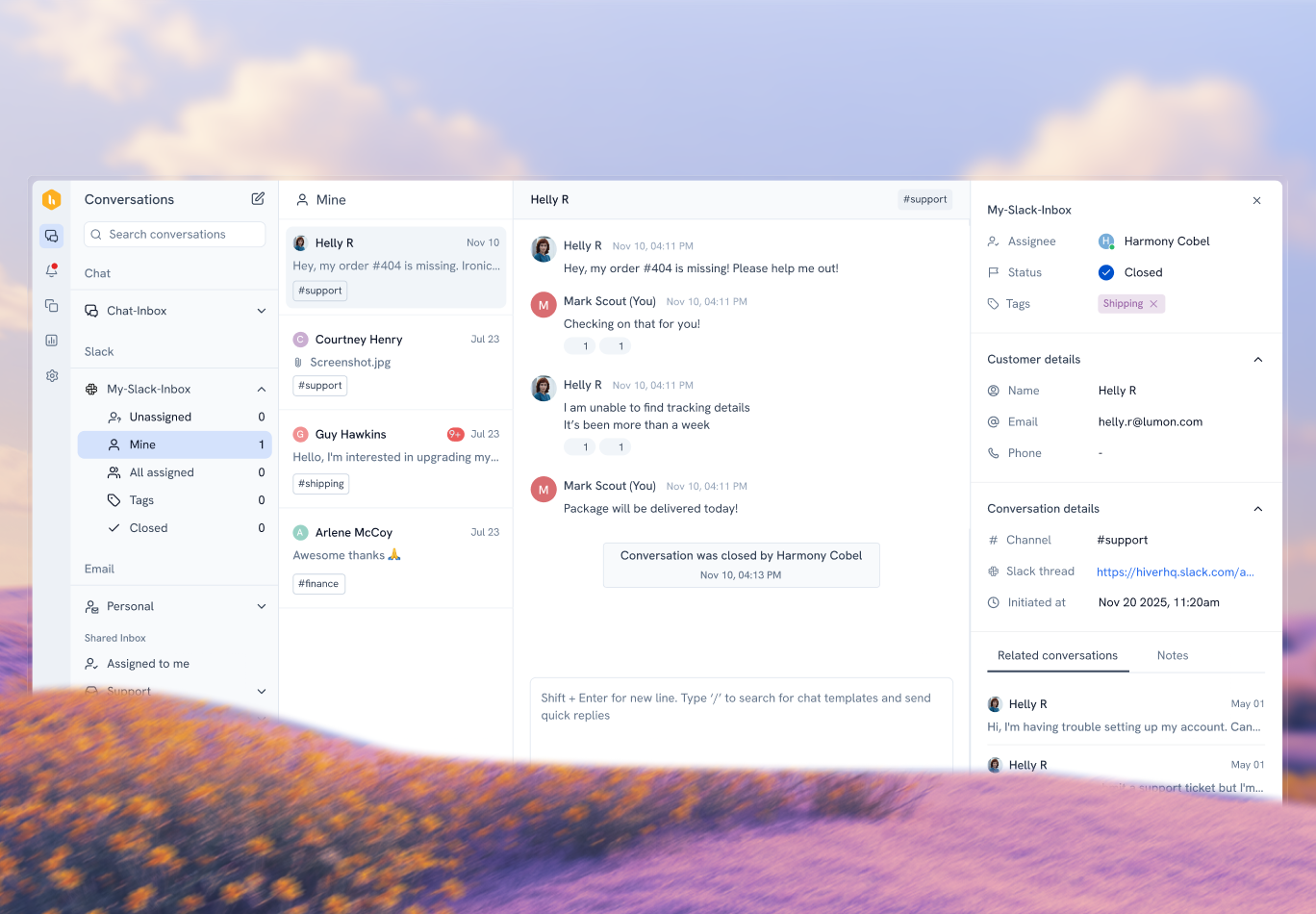
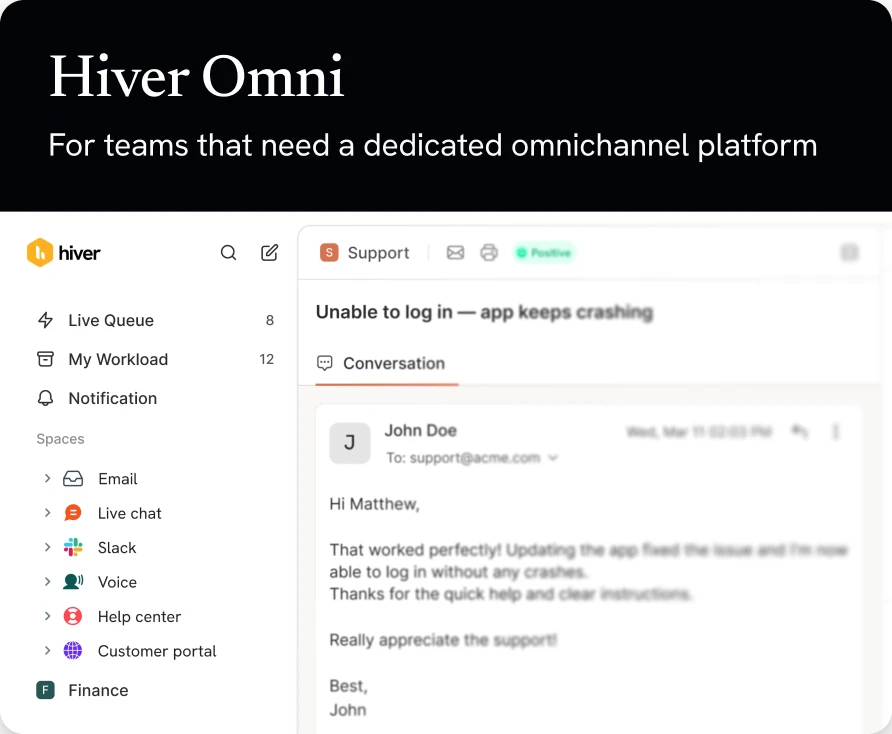
Most email security best practices focus on the perimeter: authentication, encryption, phishing filters. But for support, finance, and operations teams, the real risk often sits in shared inboxes: support@, billing@, info@. These addresses handle sensitive customer data, payment details, and account information every day. In most organizations, nobody has a clear picture of who accessed what, when a message was read, or whether a reply was sent.
This is the operational layer that technical controls alone can’t close.
Hiver addresses this directly. It adds structure and full audit visibility to shared inboxes without requiring teams to migrate to a new platform. Every incoming email has a clear owner and a tracked status. Internal notes keep sensitive discussions inside the thread rather than scattered across Slack. AI automatically tags and routes messages so nothing goes unnoticed. Collision detection prevents two agents from composing duplicate replies to the same sensitive thread simultaneously. And because every action is logged, team leads have a complete audit trail without piecing it together manually.
For teams managing compliance-sensitive communication, finance teams on billing@, legal teams on contracts@ – this operational visibility is part of the security posture. Hiver is SOC 2 Type II certified and GDPR compliant.
Best practices for auditing your email security setup
Email security isn’t something you configure once. Threats evolve, team members change, and integrations accumulate. Best practices for auditing email security setup involve reviewing configuration regularly, not only after an incident.
A practical audit checklist:
- Review third-party app permissions. In Google Workspace, go to Admin Console > Security > API Controls to see every third-party app with access to your domain’s email. Revoke anything no longer in active use. In Microsoft 365, the same review is available under Azure Active Directory > Enterprise Applications.
- Check inbox rules and filters. Attackers who compromise an account sometimes set up forwarding rules to silently redirect emails to an external address. Auditing auto-forward rules across all accounts, especially senior leaders’, should be part of any quarterly security review.
- Review login activity. Both Gmail and Outlook provide account activity logs. Logins from unrecognized locations or devices, or at unusual hours, can indicate a compromised account. Enterprise deployments can automate alerting through SIEM tools.
- Validate DMARC reporting. DMARC reports tell you who is sending email claiming to be from your domain. Reviewing these monthly surfaces unauthorized use of your domain in phishing campaigns before your customers start reporting it.
- Test your email security controls. Best practices for email security controls include periodic red team exercises or third-party penetration tests that specifically target email-based entry points. Documented results give security teams a concrete baseline to improve against.
- Audit shared inbox access and activity. For teams using shared addresses, verify that every incoming email has a documented owner, that internal notes are kept inside the thread rather than external channels, and that a full action log is available for incident response. See how it works.
Email security best practices for employees: what training should actually cover
Technology controls stop a lot. They don’t stop everything. The most reliable defense is a team that knows what a 2026 attack looks like and how to respond without panicking or ignoring it.
Effective training in 2026 covers:
- How AI-generated phishing looks different from older attacks, and why good grammar is no longer a reliable indicator of a legitimate email.
- What to do when a suspicious email arrives: report it using the built-in phishing report button, don’t just delete it. That data feeds back to security teams.
- Business email compromise red flags: any request to change payment details, redirect a wire, or grant access should be verified over the phone using a known number, not a number provided in the email.
- QR codes in email: any email containing a QR code and urging immediate action should be treated as suspicious regardless of the apparent sender.
The best free email security trainings are:
- Attack simulation training from Microsoft.
- Multiple Courses on Coursera.
Building a security-first email culture
If your team manages email across shared addresses, the operational layer is part of your security posture, not separate from it. Hiver adds audit trails, ownership tracking, and AI-powered triage so your shared inboxes are as structured and accountable as the rest of your security stack. SOC 2 Type II certified. GDPR compliant.
References
- BEC losses and overall cybercrime figures (FBI IC3 2024 Annual Report — primary source, PDF): https://www.ic3.gov/AnnualReport/Reports/2024_IC3Report.pdf
- Verizon 2025 Data Breach Investigations Report: https://www.verizon.com/business/resources/Tea/reports/2025-dbir-data-breach-investigations-report.pdf
- IBM Cost of a Data Breach 2024: https://www.ibm.com/reports/data-breach
- CISA number matching guidance (shorter fact sheet specifically on MFA fatigue mitigation): https://www.cisa.gov/resources-tools/resources/phishing-resistant-multi-factor-authentication-mfa-success-story-usdas-fast-identity-online-fido
- CIS Controls v8.1 — Control 9: Email and Web Browser Protections (the specific control that maps to the audit checklist in the article): https://www.cisecurity.org/controls/email-and-web-browser-protections
- Google Workspace — Advanced phishing and malware protection (official admin documentation): https://knowledge.workspace.google.com/admin/gmail/advanced/advanced-phishing-and-malware-protection
- Google Workspace — Security and threat prevention overview: https://workspace.google.com/security/threat-prevention/
- Microsoft 365 — Safe Attachments official documentation: https://learn.microsoft.com/en-us/defender-office-365/safe-attachments-about
- Proofpoint analysis of FBI IC3 2024 report (email as attack vector framing, useful secondary source): https://www.proofpoint.com/us/blog/email-and-cloud-threats/email-attacks-drive-record-cybercrime-losses-2024
 Skip to content
Skip to content