Security
Over 10,000+ teams globally use Hiver and they count on us to keep their data safe and secure. Hiver takes data security and privacy very seriously. We’ve especially developed processes, technologies and policies to ensure that we deliver on our data security promise.
Before we proceed, it’s essential to understand how you use Hiver or which variant you use. Hiver is available in two variants for customers, one as a Gmail extension and another as a standalone web application.
Hiver in Gmail
Hiver in Gmail is a Chrome extension that integrates directly into Gmail, transforming it into a comprehensive, modern AI-powered customer service platform. Teams continue to work from their familiar Gmail inbox, but with Hiver’s Shared Inboxes, Automations, Analytics, and AI layered on top. Hiver in Gmail only supports Gmail as an email provider.
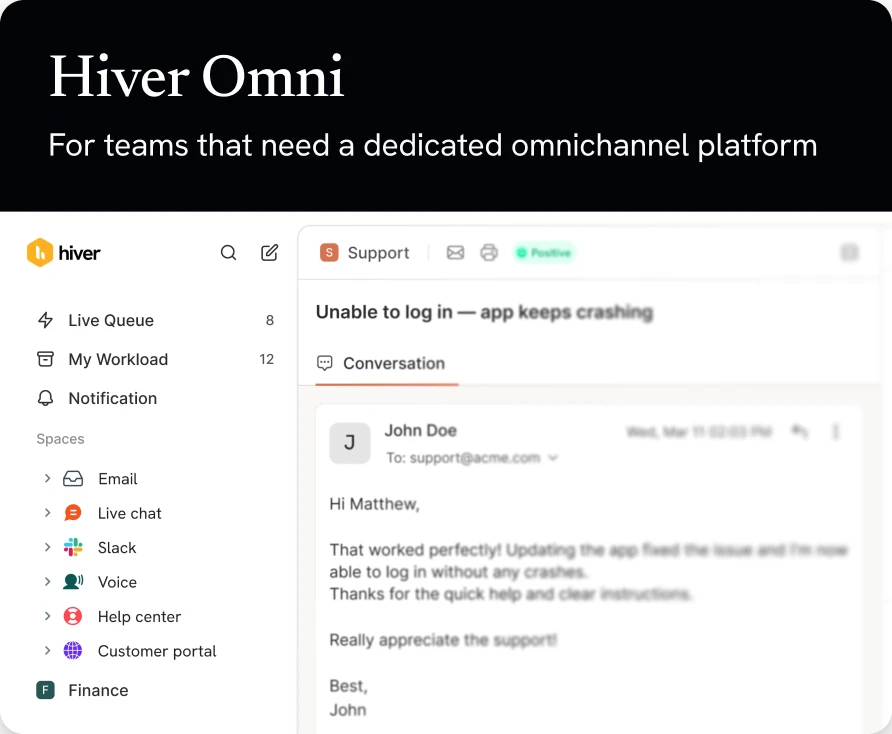
Hiver Omni
Hiver Omni is a standalone, modern AI-powered customer service platform available through a web application interface. Teams manage customer conversations across multiple channels using Hiver’s collaboration, automation, analytics, and AI. It is essential to note that Hiver Omni supports Gmail and Outlook, and will soon support additional email providers.
This document outlines some of the mechanisms and processes that we’ve implemented to keep your data safe and secure.
Transparency & Data Privacy
We believe that security policies should be absolutely transparent to the customers and the measures are outlined below.
Privacy Policy
The Hiver privacy policy is accessible at https://hiverhq.com/privacy and is strictly adhered to by all Hiver processes and our employees.
User Email data stored with Hiver
Hiver Omni
Will store and retain some data to enable our core functionality. Hiver Omni will retain Customer data for the duration of the Customer’s account, and the data will be deleted upon account closure, subject to backup schedules and applicable legal obligations, Please refer to the Clause 12 of Privacy policy – https://hiverhq.com/privacy for more details.
The data that Hiver Omni will Collect and Retain:
- Email content (message body, subject, attachments)
- Metadata (headers, message IDs, folders, labels, timestamps)
- Email account identifiers (e.g., UPN, email address, display name)
Hiver in Gmail
Does not store your emails on its servers permanently. Everything stays in your Gmail accounts. We store some of the email metadata information to enable our core functionality.
Email content we store such as:
- Message metadata (e.g., headers, labels, timestamps)
- Email account identifiers (e.g., email address, display name)
- This data is stored on Hiver’s systems to deliver Services such as shared inbox management and workflow tracking.
This information helps Hiver identify emails uniquely across your team. Apart from the above mentioned, no other email data gets stored with Hiver.
Hiver stores raw email data temporarily in an encrypted state while it syncs emails across accounts. This duration will never exceed 1 hour for 99% of the emails. When the emails have been successfully synced across Gmail accounts, the data is deleted permanently. However, For enhanced functionality and personalised experiences within Hiver Application, we may securely store your email in connection with specific features.
User data being passed to 3rd party services
Hiver engages different types of sub-processors to perform various functions including (but not limited to) storage, usage analytics, etc. The complete list of sub-processors and the purpose of processing can be found at https://hiverhq.com/third-party-subprocessors
Security Practices
Hiver adheres to the best practices in security. The measures are outlined below.
Security Policy
Hiver has an internal security policy to enforce the security practices within the team and the processes within the company. We use two factor authentication (2FA) and strong password policies on all the cloud services (AWS, Github, G Suite etc) that we use internally. We strictly control the access to customer data. Only Hiver employees who require customer data access as a necessary part of their job function are permitted to access the customer data.
Security Audits
Hiver annually engages in 3rd party security audits and we constantly scan out systems for security vulnerabilities. All access to the production servers are logged and the access is restricted to Hiver’s infrastructure team only.
Incident response policy
We have a strict policy in place about how to handle security related events, and how our team responds to them. We have monitoring tools in place which generate alerts when security events are detected and the concerned teams are notified immediately.
Vulnerability Disclosure Program
Hiver has a Vulnerability disclosure program where we encourage security researchers to report the security vulnerabilities. As a protocol,fixing reported bugs takes precedence over other tasks.
Infrastructure and Physical security
All our services and data is hosted in the USA. Hiver is hosted on Amazon web services (AWS) which are highly scalable, secure, and absolutely reliable AWS complies with leading security policy and frameworks including SAS70 level II, SSAE 16, SOC framework and ISO 27001.
To know more about how AWS manages security in its data centers, please visit https://aws.amazon.com/data-center/controls
Network Security
We implement the best practices in securing and maintaining our infrastructure. Our infrastructure is isolated from the public internet, within separate VPCs in AWS
Network Firewalls
We adhere to best practices in securing our infrastructure with network firewalls. Each of our servers uses firewalls to restrict access from external systems and between systems internally. Access is restricted to only the ports and protocols which are required by Hiver services and everything else is blocked.
TLS Encryption
The entire data transmission to or from Hiver happens over 128-bit SSL encrypted connection. Our application endpoints are TLS/SSL only and score a rating of “A+” rating on SSL Labs tests. We have taken every possible measure to keep our encryption standards meet the best practices.
Distributed Denial of service (DDOS) prevention
Hiver implements the best practices for preventing DDoS attacks. Our data centers are hosted at AWS. AWS uses a lot of Denial-of-service mitigation techniques to guard against the risk of attacks. Hiver uses the AWS Shield service too which is a managed DDoS protection service that safeguards applications running on AWS.
Storage and Backup
Hiver uses Amazon RDS as its persistent data store. Application logs, access logs and other monitoring related data are stored within AWS infrastructure on EBS disks or S3.
All application generated data is backed up automatically every few hours. Hiver keeps a copy of last database backup in encrypted state at Google’s Compute storage too. This will ensure that we will be able to restore the application within just a few hours even if there a complete AWS outage.
Data access and Authentication
Single Sign-On (SSO)
Hiver uses Single Sign-on (SSO) to login users to the Hiver applications. Hiver uses the OAuth protocol to authenticate users. The OAuth tokens to access the user’s email accounts are encrypted before getting stored. Hiver does not store any user specific passwords or any other kind of authentication detail.
Data Access
Hiver requests authorization for email data access, which is handled via the OAuth permissioning system for Gmail and Outlook accounts.
Hiver requires access to the following authentication data:
- Gmail API access for google accounts using Hiver (authenticates via OAuth). These are the permissions that Hiver requires. Read more on why Hiver needs these permissions.
- Microsoft API access for email provider accounts (authenticates via OAuth). These are the permissions that Hiver requires to get access to the email provider.
- If Hiver is installed from the Google Workspace marketplace, it requires access to the list of all Users and the list of all Groups in the organization.
Revoking access
Users and organizations can revoke Hiver access at any time:
For Microsoft accounts, access can be revoked via Microsoft account settings by the users or the Administrators.
For Google accounts, access can be revoked via Google account settings or, if installed domain-wide, via the Google Workspace admin panel.
Payment Processing
All payments are processed using Stripe. Hiver does not store customers’ credit card details.
Compliances
ISO27001
ISO 27001 specifies a management system intended to bring information security under management control and lays down specific requirements. Organizations that meet the requirements may be certified by an accredited certification body following the successful completion of an audit. You can view our ISO27001 certification here.
A part of the ISO 27000 family of standards, ISO 27001 is an information security standard, the last version of which was published in 2022.
SOC2 Type II
SOC compliance is a component of the American Institute of CPAs’ (AICPA) Service Organization Control reporting platform, intended to assure the security, availability, processing integrity, confidentiality, and privacy of customer data. SOC 2 audits are both technical and pragmatic, as they require that a company document and follow comprehensive information security policies and procedures.
The complete SOC 2 Type II report will be available upon a request sent to security@hiverhq.com under a non-disclosure commitment.
GDPR
The EU General Data Protection Regulation (GDPR) sets a new standard for how companies use and protect EU citizens’ data. It has taken effect from May 2018.
Hiver has worked diligently to prepare for GDPR, to ensure that we fulfill its obligations. We’ve now completed our GDPR readiness program and you can find more information about our compliance here.
CCPA
The California Consumer Privacy Act (CCPA) establishes and enhances consumer privacy rights for California residents and imposes rules on businesses that handle their personal information. Subject to certain limitations, the CCPA provides California residents the right to request to know more about the categories and specific pieces of personal information we collect (including how we use and disclose this information),to delete their personal information, to opt-out of any promotional activities that may be occurring and to not be discriminated against for exercising these rights.
Hiver does not sell (as the term is defined in the CCPA) the personal information we collect.
 Skip to content
Skip to content